Installing the Oz by Warp GitHub App.
There are two places you may encounter this installation flow:
Each installation is scoped to a single GitHub organization or personal account — you can install the app to multiple orgs separately.
Installing the Oz by Warp GitHub App.
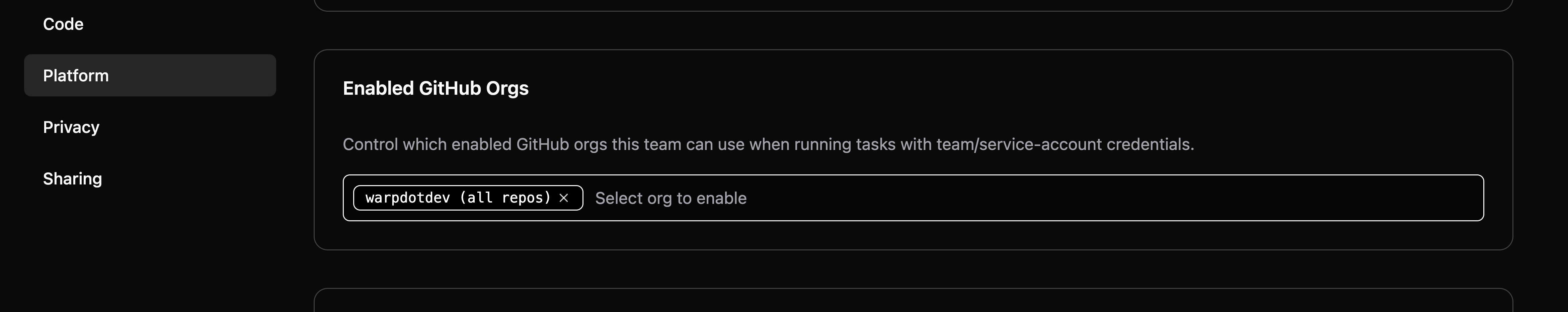
Enabled GitHub Orgs setting in the Admin Panel.